Explore the Minds of The NetSPI Agents
Advance your proactive security knowledge by learning from some of the brightest people in cybersecurity. Our executive blog gives perspective on industry trends, while Hack Responsibly dives deep into the latest CVEs and tactical approaches our team takes. Take your pick!
Our Favorite Picks

CVE-2024-21378 — Remote Code Execution in Microsoft Outlook
Learn how NetSPI discovered that Microsoft Outlook was vulnerable to authenticated remote code execution (RCE) via synced form objects.
15 Ways to Bypass the PowerShell Execution Policy
NetSPI security expert Scott Sutherland covers 15 ways to bypass the PowerShell execution policy without having local administrator rights on the system.

How to Use Attack Surface Management for Continuous Pentesting
Uncover attack surfaces and exposures with NetSPI’s offensive security including Attack Surface Management (ASM) to enable continuous pentesting.
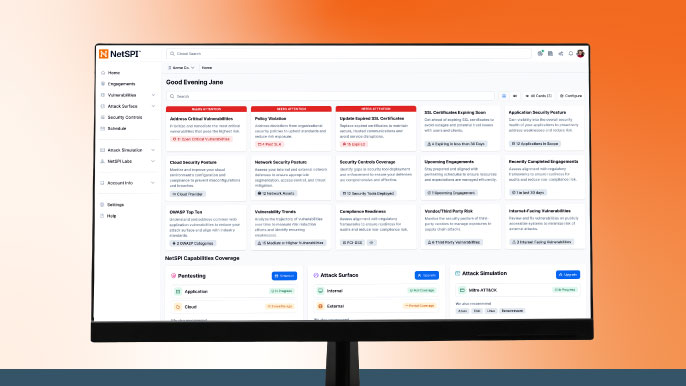
Meet NetSPI’s Modern Pentesting Experience: Use Case-Driven, AI-Accelerated
The new NetSPI experience represents the next evolution of pentesting—smarter, faster, and designed for scale.
Forrester Recognizes NetSPI in Proactive Security Landscape Report
NetSPI has been recognized among Notable Vendors in the Forrester Proactive Security Platforms Landscape, Q1 2026. Learn how we unify ASM, VRM, and pentesting.

CVE-2025-26399 SolarWinds Web Help Desk Overview and Takeaways
A critical vulnerability (CVE-2025-26399) has been identified in SolarWinds Web Help Desk, which allows unauthenticated remote attackers to execute arbitrary code on affected systems. Although CVE-2025-26399 was originally disclosed in 2025, recent reports confirm this vulnerability is now being actively exploited in the wild.
7 Ways to Execute Command on Azure Virtual Machine & Virtual Machine Scale Sets
Examples of different command execution paths for Azure Virtual Machines and Virtual Machine Scale Sets.

NetSPI Recognized for Second Consecutive Year by GigaOm
For the second consecutive year, NetSPI has been recognized in the GigaOm Radar Report for Attack Surface Management.

CVE-2026-20127 – Cisco Catalyst SD-WAN Controller and Manager Authentication Bypass Overview & Takeaways
A critical authentication bypass vulnerability (CVE-2026-20127) has been identified in Cisco Catalyst SD-WAN Controller and Manager. This flaw allows unauthenticated, remote attackers to gain administrative privileges on affected systems. Exploitation in the wild has been confirmed, and immediate action is required to mitigate risk.
Stay Ahead of Cloud Threats: Introducing Azure and AWS Security Reviews
Discover how NetSPI’s Azure & AWS Configuration Reviews provide continuous visibility, risk identification, and actionable insights to secure your cloud environments.
Ready for Red Teaming? How to Design Realistic, Intelligence-Driven Scenarios
By adopting an adversarial mindset, you can uncover the blind spots that automated scans often miss, shifting from a reactive stance to a proactive, battle-tested defense.

CVE-2026-1731 – BeyondTrust RCE Overview and Takeaways
Learn about CVE-2026-1731, a critical RCE vulnerability in BeyondTrust RS & PRA products. Discover its impact, affected versions, and remediation steps.

Pipe Dreams: Remote Code Execution via Quest Desktop Authority Named Pipe
Discover the risks of the CVE-2025-67813 vulnerability in Quest Desktop Authority. Learn how this RCE flaw impacts your organization and how to mitigate it.

Ivanti Endpoint Manager Mobile (EPMM) [CVE-2026-1281 & CVE-2026-1340]: Overview & Takeaways
Ivanti has disclosed two critical zero‑day vulnerabilities affecting Ivanti Endpoint Manager Mobile (EPMM), tracked as CVE‑2026‑1281 and CVE‑2026‑1340. Both vulnerabilities have been exploited in active attacks and allow unauthenticated remote threat actors to compromise EPMM appliances.

Why Your Security Program Needs Domain Monitoring
NetSPI Domain Monitoring continuously discovers and assesses look-alike domains related to your organization, providing deep contextual intelligence including risk profiles, WHOIS records, IP details, DNS records, and certificate data. The NetSPI Platform streamlines response, enabling rapid action against high-risk domains.
