Explore the Minds of The NetSPI Agents
Advance your proactive security knowledge by learning from some of the brightest people in cybersecurity. Our executive blog gives perspective on industry trends, while Hack Responsibly dives deep into the latest CVEs and tactical approaches our team takes. Take your pick!
Our Favorite Picks

CVE-2024-21378 — Remote Code Execution in Microsoft Outlook
Learn how NetSPI discovered that Microsoft Outlook was vulnerable to authenticated remote code execution (RCE) via synced form objects.
15 Ways to Bypass the PowerShell Execution Policy
NetSPI security expert Scott Sutherland covers 15 ways to bypass the PowerShell execution policy without having local administrator rights on the system.

How to Use Attack Surface Management for Continuous Pentesting
Uncover attack surfaces and exposures with NetSPI’s offensive security including Attack Surface Management (ASM) to enable continuous pentesting.

Walking Through an Attack Path with ForceHound
In Part 2 of the series, Weylon covers how to use ForceHound to visualize Salesforce attack paths in BloodHound CE, identify transitive privilege escalation, and legacy Connected App exposures.

Auditing Salesforce Permission Hierarchies with ForceHound
Discover how ForceHound automates the collection of profiles, permission sets, and connected apps to reveal the true trust boundaries of your Salesforce organization.

Q1 2026 Critical Vulnerability Roundup: Mitigating Risk
Discover the top critical vulnerabilities of 2026 identified by Team NetSPI and learn how proactive security measures can protect your strategic business initiatives.

Anthropic’s Mythos Announcement: What it Means for Security Teams
Anthropic’s Mythos accelerates automated vulnerability discovery. Read how to mitigate risk with custom benchmarks and human verification in your workflows.

Regulatory-Ready Security: Ensuring FCC Compliance for Routers
Last week, the FCC released a major update to the “Covered List”, officially adding foreign-produced consumer-grade routers to the registry of equipment deemed a threat to national security. This declaration was in part due to the discovery of backdoors in select routers that used standard apps in an attack chain to create a backdoor into seemingly protected networks.

CVE-2026-35616 & CVE-2026-21643 – Fortinet FortiClientEMS: Overview & Takeaways
Fortinet has disclosed two critical vulnerabilities in FortiClient Endpoint Management Server (EMS) that are both under active exploitation in the wild.
AI Fools Week: Don’t Let AI Fool Your Pentesting Strategy
AI is transforming penetration testing. It promises speed, scale, and automation. But here is the catch. When used in isolation, AI can create a false sense of security. And that is no joke. A modern approach to pentesting requires balance, combining the efficiency of AI with the expertise of human testers. Without that balance, organizations risk missing what matters most.

LiteLLM Supply Chain Compromise
A supply chain attack compromised LiteLLM versions 1.82.7 and 1.82.8 on PyPI, exfiltrating credentials and secrets to an attacker-controlled server.
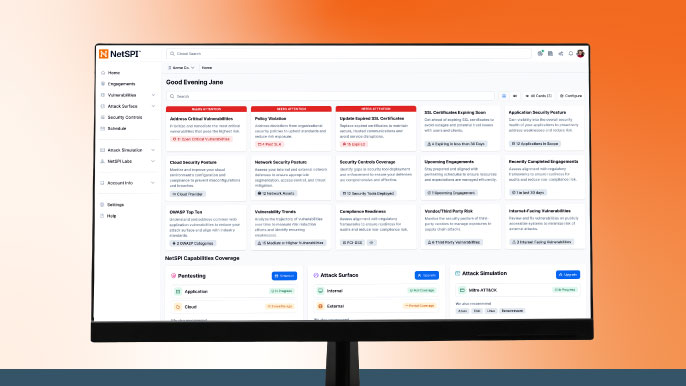
Meet NetSPI’s Modern Pentesting Experience: Use Case-Driven, AI-Accelerated
The new NetSPI experience represents the next evolution of pentesting—smarter, faster, and designed for scale.
Forrester Recognizes NetSPI in Proactive Security Landscape Report
NetSPI has been recognized among Notable Vendors in the Forrester Proactive Security Platforms Landscape, Q1 2026. Learn how we unify ASM, VRM, and pentesting.

CVE-2025-26399 SolarWinds Web Help Desk Overview and Takeaways
A critical vulnerability (CVE-2025-26399) has been identified in SolarWinds Web Help Desk, which allows unauthenticated remote attackers to execute arbitrary code on affected systems. Although CVE-2025-26399 was originally disclosed in 2025, recent reports confirm this vulnerability is now being actively exploited in the wild.
7 Ways to Execute Command on Azure Virtual Machines & Virtual Machine Scale Sets
Examples of different command execution paths for Azure Virtual Machines and Virtual Machine Scale Sets.
